Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x...
Transcript of Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x...
![Page 1: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/1.jpg)
Sparse Fourier Transform(lecture 2)
Michael Kapralov1
1IBM Watson → EPFL
St. Petersburg CS ClubNovember 2015
1 / 72
![Page 2: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/2.jpg)
Given x ∈Cn, compute the Discrete Fourier Transform of x :
xf =1n
∑j∈[n]
xjω−f ·j ,
where ω= e2πi/n is the n-th root of unity.
Goal: find the top k coefficients of x approximately
In last lecture:
Ï 1-sparse noiseless case: two-point sampling
Ï 1-sparse noisy case: O(logn loglogn) time and samples
Ï reduction from k -sparse to 1-sparse case, via filtering
2 / 72
![Page 3: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/3.jpg)
Given x ∈Cn, compute the Discrete Fourier Transform of x :
xf =1n
∑j∈[n]
xjω−f ·j ,
where ω= e2πi/n is the n-th root of unity.
Goal: find the top k coefficients of x approximately
In last lecture:
Ï 1-sparse noiseless case: two-point sampling
Ï 1-sparse noisy case: O(logn loglogn) time and samples
Ï reduction from k -sparse to 1-sparse case, via filtering
2 / 72
![Page 4: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/4.jpg)
Given x ∈Cn, compute the Discrete Fourier Transform of x :
xf =1n
∑j∈[n]
xjω−f ·j ,
where ω= e2πi/n is the n-th root of unity.
Goal: find the top k coefficients of x approximately
In last lecture:
Ï 1-sparse noiseless case: two-point sampling
Ï 1-sparse noisy case: O(logn loglogn) time and samples
Ï reduction from k -sparse to 1-sparse case, via filtering
2 / 72
![Page 5: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/5.jpg)
Given x ∈Cn, compute the Discrete Fourier Transform of x :
xf =1n
∑j∈[n]
xjω−f ·j ,
where ω= e2πi/n is the n-th root of unity.
Goal: find the top k coefficients of x approximately
In last lecture:
Ï 1-sparse noiseless case: two-point sampling
Ï 1-sparse noisy case: O(logn loglogn) time and samples
Ï reduction from k -sparse to 1-sparse case, via filtering
2 / 72
![Page 6: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/6.jpg)
Partition frequency domain into B ≈ k buckets
-0.001
-0.0005
0
0.0005
0.001
-1000 -500 0 500 1000
time
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
For each j = 0, . . . ,B−1 let
ujf =
xf , if f ∈ j-th bucket0 o.w.
Restricted to a bucket, signal is likely approximately 1-sparse!
3 / 72
![Page 7: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/7.jpg)
Partition frequency domain into B ≈ k buckets
-0.001
-0.0005
0
0.0005
0.001
-1000 -500 0 500 1000
time
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
For each j = 0, . . . ,B−1 let
ujf =
xf , if f ∈ j-th bucket0 o.w.
Restricted to a bucket, signal is likely approximately 1-sparse!
4 / 72
![Page 8: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/8.jpg)
Partition frequency domain into B ≈ k buckets
-0.001
-0.0005
0
0.0005
0.001
-1000 -500 0 500 1000
time
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
For each j = 0, . . . ,B−1 let
ujf =
xf , if f ∈ j-th bucket0 o.w.
Restricted to a bucket, signal is likely approximately 1-sparse!
4 / 72
![Page 9: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/9.jpg)
Partition frequency domain into B ≈ k buckets
-0.0008
-0.0006
-0.0004
-0.0002
0
0.0002
0.0004
0.0006
0.0008
-1000 -500 0 500 1000
time
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
For each j = 0, . . . ,B−1 let
ujf =
xf , if f ∈ j-th bucket0 o.w.
Restricted to a bucket, signal is likely approximately 1-sparse!
5 / 72
![Page 10: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/10.jpg)
Partition frequency domain into B ≈ k buckets
-0.0008
-0.0006
-0.0004
-0.0002
0
0.0002
0.0004
0.0006
0.0008
-1000 -500 0 500 1000
time
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
For each j = 0, . . . ,B−1 let
ujf =
xf , if f ∈ j-th bucket0 o.w.
Restricted to a bucket, signal is likely approximately 1-sparse!
6 / 72
![Page 11: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/11.jpg)
Partition frequency domain into B ≈ k buckets
-0.0008
-0.0006
-0.0004
-0.0002
0
0.0002
0.0004
0.0006
0.0008
-1000 -500 0 500 1000
time
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
For each j = 0, . . . ,B−1 let
ujf =
xf , if f ∈ j-th bucket0 o.w.
Restricted to a bucket, signal is likely approximately 1-sparse!
6 / 72
![Page 12: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/12.jpg)
Partition frequency domain into B ≈ k buckets
-0.0008
-0.0006
-0.0004
-0.0002
0
0.0002
0.0004
0.0006
0.0008
-1000 -500 0 500 1000
time
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
For each j = 0, . . . ,B−1 let
ujf =
xf , if f ∈ j-th bucket0 o.w.
Restricted to a bucket, signal is likely approximately 1-sparse!
6 / 72
![Page 13: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/13.jpg)
Partition frequency domain into B ≈ k buckets
-0.0008
-0.0006
-0.0004
-0.0002
0
0.0002
0.0004
0.0006
0.0008
-1000 -500 0 500 1000
time
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
For each j = 0, . . . ,B−1 let
ujf =
xf , if f ∈ j-th bucket0 o.w.
Restricted to a bucket, signal is likely approximately 1-sparse!
6 / 72
![Page 14: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/14.jpg)
Partition frequency domain into B ≈ k buckets
-0.0008
-0.0006
-0.0004
-0.0002
0
0.0002
0.0004
0.0006
0.0008
-1000 -500 0 500 1000
time
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
For each j = 0, . . . ,B−1 let
ujf =
xf , if f ∈ j-th bucket0 o.w.
Restricted to a bucket, signal is likely approximately 1-sparse!
6 / 72
![Page 15: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/15.jpg)
Partition frequency domain into B ≈ k buckets
-0.0008
-0.0006
-0.0004
-0.0002
0
0.0002
0.0004
0.0006
0.0008
-1000 -500 0 500 1000
time
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
For each j = 0, . . . ,B−1 let
ujf =
xf , if f ∈ j-th bucket0 o.w.
Restricted to a bucket, signal is likely approximately 1-sparse!
6 / 72
![Page 16: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/16.jpg)
We want time domain access to u0: for any a= 0, . . . ,n−1,compute
u0a = ∑
− n2B ≤f≤ n
2B
xf ·ωf ·a.
Let
Gf =
1, if f ∈ [− n2B : n
2B]
0 o.w.
Thenu0
a = (x·+a ∗ G)(0)
For any j = 0, . . . ,B−1
uja = (x·+a ∗ G)(j · n
B)
7 / 72
![Page 17: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/17.jpg)
We want time domain access to u0: for any a= 0, . . . ,n−1,compute
u0a = ∑
− n2B ≤f≤ n
2B
xf ·ωf ·a.
Let
Gf =
1, if f ∈ [− n2B : n
2B]
0 o.w.
Thenu0
a = (x·+a ∗ G)(0)
For any j = 0, . . . ,B−1
uja = (x·+a ∗ G)(j · n
B)
7 / 72
![Page 18: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/18.jpg)
Reducing k -sparse recovery to 1-sparse recovery
For any j = 0, . . . ,B−1
uja = (x·+a ∗ G)(j · n
B)
−1000 −800 −600 −400 −200 0 200 400 600 800 1000−2.5
−2
−1.5
−1
−0.5
0
0.5
1
1.5
2
2.5
time
magnitu
de
−1000 −800 −600 −400 −200 0 200 400 600 800 1000−0.2
0
0.2
0.4
0.6
0.8
1
frequency
magnitu
de
8 / 72
![Page 19: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/19.jpg)
Reducing k -sparse recovery to 1-sparse recovery
For any j = 0, . . . ,B−1
uja = (x·+a ∗ G)(j · n
B)
−1000 −800 −600 −400 −200 0 200 400 600 800 1000−2.5
−2
−1.5
−1
−0.5
0
0.5
1
1.5
2
2.5
time
magnitu
de
−1000 −800 −600 −400 −200 0 200 400 600 800 1000−0.2
0
0.2
0.4
0.6
0.8
1
frequency
magnitu
de
9 / 72
![Page 20: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/20.jpg)
Reducing k -sparse recovery to 1-sparse recovery
For any j = 0, . . . ,B−1
uja = (x·+a ∗ G)(j · n
B)
−1000 −800 −600 −400 −200 0 200 400 600 800 1000−2.5
−2
−1.5
−1
−0.5
0
0.5
1
1.5
2
2.5
time
magnitu
de
−1000 −800 −600 −400 −200 0 200 400 600 800 1000−0.2
0
0.2
0.4
0.6
0.8
1
frequency
magnitu
de
10 / 72
![Page 21: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/21.jpg)
Need to evaluate(x·+a ∗ G)
(j · n
B
)for j = 0, . . . ,B−1.
We have access to x , not x ...
By the convolution identity
x·+a ∗ G = á(x·+a ·G)
Suffices to compute
àx·+a ·Gj · nB
, j = 0, . . . ,B−1
11 / 72
![Page 22: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/22.jpg)
Need to evaluate(x·+a ∗ G)
(j · n
B
)for j = 0, . . . ,B−1.
We have access to x , not x ...
By the convolution identity
x·+a ∗ G = á(x·+a ·G)
Suffices to compute
àx·+a ·Gj · nB
, j = 0, . . . ,B−1
11 / 72
![Page 23: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/23.jpg)
Need to evaluate(x·+a ∗ G)
(j · n
B
)for j = 0, . . . ,B−1.
We have access to x , not x ...
By the convolution identity
x·+a ∗ G = á(x·+a ·G)
Suffices to compute
àx·+a ·Gj · nB
, j = 0, . . . ,B−1
11 / 72
![Page 24: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/24.jpg)
Suffices to compute
àx·+a ·Gj · nB
, j = 0, . . . ,B−1
Sample complexity? Runtime?
-0.4
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
time
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
frequency
Computing x ·G takes Ω(N) time and samples!
11 / 72
![Page 25: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/25.jpg)
Suffices to compute
x ·Gj · nB
, j = 0, . . . ,B−1
Sample complexity? Runtime?
-0.4
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
time
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
frequency
Computing x ·G takes Ω(N) time and samples!
11 / 72
![Page 26: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/26.jpg)
Suffices to compute
x ·Gj · nB
, j = 0, . . . ,B−1
Sample complexity? Runtime?
-0.4
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
time
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
frequency
Computing x ·G takes Ω(N) time and samples!
11 / 72
![Page 27: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/27.jpg)
Suffices to compute
x ·Gj · nB
, j = 0, . . . ,B−1
Sample complexity? Runtime?
-0.4
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
time
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
frequency
Computing x ·G takes Ω(N) time and samples!
11 / 72
![Page 28: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/28.jpg)
To sample all signals uj , j = 0, . . . ,B−1 in time domain, it sufficesto compute x ·Gj · n
B, j = 0, . . . ,B−1
-0.4
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
time
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
frequency
Computing x ·G takes supp(G) samples.
Design G with supp(G)≈ k that approximates rectangular filter?
11 / 72
![Page 29: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/29.jpg)
In this lecture:
Ï permuting frequencies
Ï filter construction
12 / 72
![Page 30: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/30.jpg)
1. Pseudorandom spectrum permutations
2. Filter construction
13 / 72
![Page 31: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/31.jpg)
1. Pseudorandom spectrum permutations
2. Filter construction
14 / 72
![Page 32: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/32.jpg)
Pseudorandom spectrum permutationsPermutation in time domain plus phase shift =⇒ permutation infrequency domain
ClaimLet σ,b ∈ [n], σ invertible modulo n. Let yj = xσjω
−jb. Then
yf = xσ−1(f+b).
(proof on next slide; a close relative of time shift theorem)
Pseudorandom permutation:
Ï select b uniformly at random from [n]
Ï select σ uniformly at random from 1,3,5, . . . ,n−1(invertible numbers modulo n)
15 / 72
![Page 33: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/33.jpg)
Pseudorandom spectrum permutationsPermutation in time domain plus phase shift =⇒ permutation infrequency domain
ClaimLet σ,b ∈ [n], σ invertible modulo n. Let yj = xσjω
−jb. Then
yf = xσ−1(f+b).
(proof on next slide; a close relative of time shift theorem)
Pseudorandom permutation:
Ï select b uniformly at random from [n]
Ï select σ uniformly at random from 1,3,5, . . . ,n−1(invertible numbers modulo n)
15 / 72
![Page 34: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/34.jpg)
Pseudorandom spectrum permutationsPermutation in time domain plus phase shift =⇒ permutation infrequency domain
ClaimLet σ,b ∈ [n], σ invertible modulo n. Let yj = xσjω
−jb. Then
yf = xσ−1(f+b).
(proof on next slide; a close relative of time shift theorem)
Pseudorandom permutation:
Ï select b uniformly at random from [n]
Ï select σ uniformly at random from 1,3,5, . . . ,n−1(invertible numbers modulo n)
15 / 72
![Page 35: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/35.jpg)
Pseudorandom spectrum permutationsClaimLet yj = xσjω
−jb. Then yf = xσ−1(f+b).
Proof.
yf =1n
∑j∈[n]
yjω−f ·j
= 1n
∑j∈[n]
xσjω−(f+b)·j
= 1n
∑i∈[n]
xiω−(f+b)·σ−1i (change of variables i =σj)
= 1n
∑i∈[n]
xiω−σ−1(f+b)·i
= xσ−1(f+b)
16 / 72
![Page 36: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/36.jpg)
-0.4
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
time
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
frequency
Design G with supp(G)≈ k that approximates rectangular filter?
Our filter G will approximate the boxcar. Bound collisionprobability now.
16 / 72
![Page 37: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/37.jpg)
Partition frequency domain into buckets, permute spectrum
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
Frequency i collides with frequency j only if |σi −σj | ≤ nB .
17 / 72
![Page 38: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/38.jpg)
Partition frequency domain into buckets, permute spectrum
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
Frequency i collides with frequency j only if |σi −σj | ≤ nB .
18 / 72
![Page 39: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/39.jpg)
Partition frequency domain into buckets, permute spectrum
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
Frequency i collides with frequency j only if |σi −σj | ≤ nB .
19 / 72
![Page 40: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/40.jpg)
Partition frequency domain into buckets, permute spectrum
-0.5
0
0.5
1
-1000 -500 0 500 1000
frequency
collision
Frequency i collides with frequency j only if |σi −σj | ≤ nB .
20 / 72
![Page 41: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/41.jpg)
Collision probabilityLemmaLet σ be a uniformly random odd number in 1,2, . . . ,n. Then forany i , j ∈ [n], i 6= j one has
Prσ[|σ · i −σj | ≤ n
B
]=O(1/B)
Proof.Let ∆ := i − j = d2s for some odd d .
The orbit of σ ·∆ is 2s ·d ′ for all odd d ′.
[ ]σi − n
Bσi σi + n
B
There are O( n
B2s
)values of d ′ that make σ ·∆ fall into
[− nB , n
B],
out of n/2s+1.
21 / 72
![Page 42: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/42.jpg)
Collision probabilityLemmaLet σ be a uniformly random odd number in 1,2, . . . ,n. Then forany i , j ∈ [n], i 6= j one has
Prσ[|σ · i −σj | ≤ n
B
]=O(1/B)
Proof.Let ∆ := i − j = d2s for some odd d .
The orbit of σ ·∆ is 2s ·d ′ for all odd d ′.
[ ]σi − n
Bσi σi + n
B
There are O( n
B2s
)values of d ′ that make σ ·∆ fall into
[− nB , n
B],
out of n/2s+1.21 / 72
![Page 43: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/43.jpg)
Collision probabilityLemmaLet σ be a uniformly random odd number in 1,2, . . . ,n. Then forany i , j ∈ [n], i 6= j one has
Prσ[|σ · i −σj | ≤ n
B
]=O(1/B)
Proof.Let ∆ := i − j = d2s for some odd d .
The orbit of σ ·∆ is 2s ·d ′ for all odd d ′.
[ ]σi − n
Bσi σi + n
B
There are O( n
B2s
)values of d ′ that make σ ·∆ fall into
[− nB , n
B],
out of n/2s+1.21 / 72
![Page 44: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/44.jpg)
Collision probabilityLemmaLet σ be a uniformly random odd number in 1,2, . . . ,n. Then forany i , j ∈ [n], i 6= j one has
Prσ[|σ · i −σj | ≤ n
B
]=O(1/B)
Proof.Let ∆ := i − j = d2s for some odd d .
The orbit of σ ·∆ is 2s ·d ′ for all odd d ′.
[ ]σi − n
Bσi σi + n
B
There are O( n
B2s
)values of d ′ that make σ ·∆ fall into
[− nB , n
B],
out of n/2s+1.21 / 72
![Page 45: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/45.jpg)
Collision probabilityLemmaLet σ be a uniformly random odd number in 1,2, . . . ,n. Then forany i , j ∈ [n], i 6= j one has
Prσ[|σ · i −σj | ≤ n
B
]=O(1/B)
Proof.Let ∆ := i − j = d2s for some odd d .
The orbit of σ ·∆ is 2s ·d ′ for all odd d ′.
[ ]σi − n
Bσi σi + n
B
There are O( n
B2s
)values of d ′ that make σ ·∆ fall into
[− nB , n
B],
out of n/2s+1.21 / 72
![Page 46: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/46.jpg)
1. Pseudorandom spectrum permutations
2. Filter construction
22 / 72
![Page 47: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/47.jpg)
Rectangular buckets G have full support in time domain...
-0.4
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
time
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
frequency
Approximate rectangular filter with a filter G with small support?
Need supp(G)≈ k , so perhaps turn the filter around?
23 / 72
![Page 48: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/48.jpg)
Let
Gj :=
1/(B+1) if j ∈ [−B/2,B/2]0 o.w.
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
time
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
Have supp(G)=B ≈ k , but buckets leak
24 / 72
![Page 49: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/49.jpg)
=⇒
In what follows: reduce leakage at the expense of increasingsupp(G)
25 / 72
![Page 50: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/50.jpg)
Window functionsDefinitionA symmetric filter G is a (B,δ)-standard window function if
1. G0 = 12. Gf ≥ 03. |Gf | ≤ δ for f 6∈ [− n
2B , n2B
]
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
26 / 72
![Page 51: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/51.jpg)
Window functions
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
Start with the sinc function:
Gf :=sin(π(B+1)f/n)(B+1) ·πf/n
For all |f | > n2B we have
|Gf | ≤1
(B+1)πf/n≤ 1π/2
≤ 2/π≤ 0.9
27 / 72
![Page 52: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/52.jpg)
Window functions
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
Start with the sinc function:
Gf :=sin(π(B+1)f/n)(B+1) ·πf/n
For all |f | > n2B we have
|Gf | ≤1
(B+1)πf/n≤ 1π/2
≤ 2/π≤ 0.9
27 / 72
![Page 53: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/53.jpg)
Window functions
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
Consider powers of the sinc function:
Grf :=
(sin(π(B+1)f/n)(B+1) ·πf/n
)r
For all |f | > n2B we have
|Gf |r ≤ (0.9)r
28 / 72
![Page 54: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/54.jpg)
Window functions
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
Consider powers of the sinc function:
Grf :=
(sin(π(B+1)f/n)(B+1) ·πf/n
)r
For all |f | > n2B we have
|Gf |r ≤ (0.9)r
29 / 72
![Page 55: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/55.jpg)
Window functions
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
Consider powers of the sinc function: Grf
For all |f | > n2B we have
|Gf |r ≤ (0.9)r
So setting r =O(log(1/δ)) is sufficient!
30 / 72
![Page 56: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/56.jpg)
Window functions
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
Consider powers of the sinc function: Grf
For all |f | > n2B we have
|Gf |r ≤ (0.9)r
So setting r =O(log(1/δ)) is sufficient!31 / 72
![Page 57: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/57.jpg)
Window functionsDefinitionA symmetric filter G is a (B,δ)-standard window function if
1. G0 = 12. Gf ≥ 03. |Gf | ≤ δ for f 6∈ [− n
2B , n2B
]
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
32 / 72
![Page 58: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/58.jpg)
Window functionsDefinitionA symmetric filter G is a (B,δ)-standard window function if
1. G0 = 12. Gf ≥ 03. |Gf | ≤ δ for f 6∈ [− n
2B , n2B
]
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
How large is supp(G)⊆ [−T ,T ]? 33 / 72
![Page 59: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/59.jpg)
Let
Gj :=
1/(B+1) if j ∈ [−B/2,B/2]0 o.w.
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
time
Let Gr := (G0)r . How large is the support of Gr ?
By the convolution identity Gr =G0 ∗G0 ∗ . . .∗G0
Support of G0 is in [−B/2,B/2], so
supp(G∗ . . .∗G)⊆ [−r ·B/2,r ·B/2]
33 / 72
![Page 60: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/60.jpg)
Let
Gj :=
1/(B+1) if j ∈ [−B/2,B/2]0 o.w.
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
time
Let Gr := (G0)r . How large is the support of Gr ?
By the convolution identity Gr =G0 ∗G0 ∗ . . .∗G0
Support of G0 is in [−B/2,B/2], so
supp(G∗ . . .∗G)⊆ [−r ·B/2,r ·B/2]
32 / 72
![Page 61: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/61.jpg)
Let
Gj :=
1/(B+1) if j ∈ [−B/2,B/2]0 o.w.
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
time
Let Gr := (G0)r . How large is the support of Gr ?
By the convolution identity Gr =G0 ∗G0 ∗ . . .∗G0
Support of G0 is in [−B/2,B/2], so
supp(G∗ . . .∗G)⊆ [−r ·B/2,r ·B/2]
31 / 72
![Page 62: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/62.jpg)
Let
Gj :=
1/(B+1) if j ∈ [−B/2,B/2]0 o.w.
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
time
Let Gr := (G0)r . How large is the support of Gr ?
By the convolution identity Gr =G0 ∗G0 ∗ . . .∗G0
Support of G0 is in [−B/2,B/2], so
supp(G∗ . . .∗G)⊆ [−r ·B/2,r ·B/2]
31 / 72
![Page 63: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/63.jpg)
Let
Gj :=
1/(B+1) if j ∈ [−B/2,B/2]0 o.w.
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
time
Let Gr := (G0)r . How large is the support of Gr ?
By the convolution identity Gr =G0 ∗G0 ∗ . . .∗G0
Support of G0 is in [−B/2,B/2], so
supp(G∗ . . .∗G)⊆ [−r ·B/2,r ·B/2]
31 / 72
![Page 64: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/64.jpg)
Let
Gj :=
1/(B+1) if j ∈ [−B/2,B/2]0 o.w.
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
time
Let Gr := (G0)r . How large is the support of Gr ?
By the convolution identity Gr =G0 ∗G0 ∗ . . .∗G0
Support of G0 is in [−B/2,B/2], so
supp(G∗ . . .∗G)⊆ [−r ·B/2,r ·B/2]
31 / 72
![Page 65: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/65.jpg)
Let
Gj :=
1/(B+1) if j ∈ [−B/2,B/2]0 o.w.
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
time
Let Gr := (G0)r . How large is the support of Gr ?
By the convolution identity Gr =G0 ∗G0 ∗ . . .∗G0
Support of G0 is in [−B/2,B/2], so
supp(G∗ . . .∗G)⊆ [−r ·B/2,r ·B/2]
31 / 72
![Page 66: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/66.jpg)
Let
Gj :=
1/(B+1) if j ∈ [−B/2,B/2]0 o.w.
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
time
Let Gr := (G0)r . How large is the support of Gr ?
By the convolution identity Gr =G0 ∗G0 ∗ . . .∗G0
Support of G0 is in [−B/2,B/2], so
supp(G∗ . . .∗G)⊆ [−r ·B/2,r ·B/2]
31 / 72
![Page 67: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/67.jpg)
Let
Gj :=
1/(B+1) if j ∈ [−B/2,B/2]0 o.w.
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
0
0.2
0.4
0.6
0.8
1
1.2
-1000 -500 0 500 1000
time
Let Gr := (G0)r . How large is the support of Gr ?
By the convolution identity Gr =G0 ∗G0 ∗ . . .∗G0
Support of G0 is in [−B/2,B/2], so
supp(G∗ . . .∗G)⊆ [−r ·B/2,r ·B/2]
31 / 72
![Page 68: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/68.jpg)
Flat window functionDefinitionA symmetric filter G is a (B,δ,γ)-flat window function if
1. Gj ≥ 1−δ for all j ∈ [−(1−γ) n2B ,(1−γ) n
2B]
2. Gj ∈ [0,1] for all j
3. |Gf | ≤ δ for f 6∈ [− n2B , n
2B]
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
32 / 72
![Page 69: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/69.jpg)
Flat window functionDefinitionA symmetric filter G is a (B,δ,γ)-flat window function if
1. Gj ≥ 1−δ for all j ∈ [−(1−γ) n2B ,(1−γ) n
2B]
2. Gj ∈ [0,1] for all j
3. |Gf | ≤ δ for f 6∈ [− n2B , n
2B]
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
33 / 72
![Page 70: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/70.jpg)
Flat window functionDefinitionA symmetric filter G is a (B,δ,γ)-flat window function if
1. Gj ≥ 1−δ for all j ∈ [−(1−γ) n2B ,(1−γ) n
2B]
2. Gj ∈ [0,1] for all j
3. |Gf | ≤ δ for f 6∈ [− n2B , n
2B]
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
0.99 fraction of bucket
34 / 72
![Page 71: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/71.jpg)
Flat window function – construction
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
Let H be a (2B/γ,δ/n)-standard window function. Note that
|Hf | ≤ δ/n
for all f outside of [−γ n
4B,γ
n4B
].
35 / 72
![Page 72: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/72.jpg)
Flat window function – construction
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
1−γ/2 fraction of bucket
Let H be a (2B/γ,δ/n)-standard window function. Note that
|Hf | ≤ δ/n
for all f outside of [−γ n
4B,γ
n4B
].
36 / 72
![Page 73: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/73.jpg)
Flat window function – construction
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
Let H be a (2B/γ,δ/n)-standard window function. Note that
|Hf | ≤ δ/n
for all f outside of [−γ n
4B,γ
n4B
].
37 / 72
![Page 74: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/74.jpg)
Flat window function – construction
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
Let H be a (2B/γ,δ/n)-standard window function. Note that
|Hf | ≤ δ/n
for all f outside of [−γ n
4B,γ
n4B
].
38 / 72
![Page 75: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/75.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
39 / 72
![Page 76: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/76.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
39 / 72
![Page 77: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/77.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
39 / 72
![Page 78: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/78.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
39 / 72
![Page 79: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/79.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
40 / 72
![Page 80: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/80.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
40 / 72
![Page 81: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/81.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
41 / 72
![Page 82: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/82.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
41 / 72
![Page 83: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/83.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
41 / 72
![Page 84: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/84.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
41 / 72
![Page 85: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/85.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
41 / 72
![Page 86: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/86.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
41 / 72
![Page 87: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/87.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
41 / 72
![Page 88: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/88.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
41 / 72
![Page 89: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/89.jpg)
Flat window function – constructionTo construct G:
1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B2. normalize so that G0 = 1±δ
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
41 / 72
![Page 90: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/90.jpg)
To construct G:1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B
2. normalize so that G0 = 1±δ
Formally:
Gf :=1Z
(H f−U + H f+1−U + . . .+ H f+U
)where Z is a normalization factor.
Upon inspection, Z =∑f∈[n] Hf works.
42 / 72
![Page 91: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/91.jpg)
To construct G:1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B
2. normalize so that G0 = 1±δ
Formally:
Gf :=1Z
(H f−U + H f+1−U + . . .+ H f+U
)where Z is a normalization factor.
Upon inspection, Z =∑f∈[n] Hf works.
42 / 72
![Page 92: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/92.jpg)
To construct G:1. sum up shifts H ·−∆ over all ∆ ∈ [−U ,U], where
U = (1−γ/2)n
2B
2. normalize so that G0 = 1±δ
Formally:
Gf :=1Z
(H f−U + H f+1−U + . . .+ H f+U
)where Z is a normalization factor.
Upon inspection, Z =∑f∈[n] Hf works.
43 / 72
![Page 93: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/93.jpg)
Formally:
Gf :=1Z
(H f−U + H f+1−U + . . .+ H f+U
)where Z is a normalization factor.
Upon inspection, Z =∑f∈[n] Hf works.
(Flat region) For any f ∈ [−(1−γ) n2B ,(1−γ) n
2B ] (flat region) onehas
H f−U + H f+1−U + . . .+ H f+U ≥ ∑f∈[−γ n
4B ,γ n4B ]
Hf
≥Z − tail of H≥Z − (δ/n)n ≥Z −δ
44 / 72
![Page 94: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/94.jpg)
Formally:
Gf :=1Z
(H f−U + H f+1−U + . . .+ H f+U
)where Z is a normalization factor.
Upon inspection, Z =∑f∈[n] Hf works.
Indeed, for any f 6∈ [− n2B , n
2B ] (zero region) one has
H f−U + H f+1−U + . . .+ H f+U ≤ ∑f>γ n
4B
Hf
≤ tail of H ≤ (δ/n)n ≤ δ
45 / 72
![Page 95: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/95.jpg)
Flat window function
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
How large is support of G := 1Z
(H ·−U + . . .+ H ·+U
)?
By time shift theorem for every q ∈ [n]
Gq :=Hq · 1Z
U∑j=−U
ωqj
Support of G a subset of support of H!
46 / 72
![Page 96: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/96.jpg)
Flat window function
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
How large is support of G := 1Z
(H ·−U + . . .+ H ·+U
)?
By time shift theorem for every q ∈ [n]
Gq :=Hq · 1Z
U∑j=−U
ωqj
Support of G a subset of support of H!
46 / 72
![Page 97: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/97.jpg)
Flat window function
− n2B 0 n
2B
ideal bucket
leakage to other buckets
bounded by δ¿ 1
1−γ fraction of bucket
How large is support of G := 1Z
(H ·−U + . . .+ H ·+U
)?
By time shift theorem for every q ∈ [n]
Gq :=Hq · 1Z
U∑j=−U
ωqj
Support of G a subset of support of H!46 / 72
![Page 98: Sparse Fourier Transform (lecture 2) - EPFLtheory.epfl.ch/kapralov/sfft-minicourse15/lec2.pdfGiven x 2Cn, compute the Discrete Fourier Transform of x: bxf ˘ 1 n X j2[n] xj! ¡f¢j,](https://reader034.fdocument.org/reader034/viewer/2022051909/5ffd36d446a5cc3e553729d8/html5/thumbnails/98.jpg)
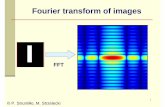
Flat window functions – construction
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
*
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
=
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
-0.2
0
0.2
0.4
0.6
0.8
1
-1000 -500 0 500 1000
frequency
47 / 72







![[Solutions Manual] Fourier and Laplace Transform - Antwoorden](https://static.fdocument.org/doc/165x107/5529e0de4a7959eb768b45f9/solutions-manual-fourier-and-laplace-transform-antwoorden.jpg)