Part 1: Fuzzy extractor based on universal hashes Part 2: Simplification of Controlled PUF...
-
date post
18-Dec-2015 -
Category
Documents
-
view
216 -
download
0
Transcript of Part 1: Fuzzy extractor based on universal hashes Part 2: Simplification of Controlled PUF...
Part 1:Fuzzy extractor based on universal hashes
Part 2:Simplification of Controlled PUF primitives
Dagstuhl, July 6-8, 20091
Fuzzy Extractor / Helper Data scheme
3
Properties
• Secrecy and uniformity: Δ(WS; WU) ≤ ε. "S given W is almost uniform"
• Error correction: If X' sufficiently close to X, then S'=S.
• Robustness [Boyen et al. 2005]: Detection of active attack against W
noisy
Dodis et al. 2003Juels+Wattenberg 1999Linnartz+Tuyls 2003
Applications
• privacy preserving biometrics
• anti-counterfeiting ("object biometrics")
• PUF-based key storage
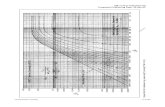
Fuzzy Extractor: Efficiency
noisy
What's so special?
• Redundancy data (in W) must not leak info about secret S.
• Make near-uniform S from non-uniform X.
• How to authenticate W when there is no PKI?
"Efficiency"
• Extract as many reproducible bits from X as possible.
• Low storage requirements.
• Small computational load.
4
5
Limited noise
Common class of noise
• Considerable prob. that x' ≠ x.
• Small number of likely x'.
x
x'
Example
Problematic for error correcting codes
• Most codes work best with low error rate
• Cannot exploit non-uniform error patterns (low entropy of errors)
• Entropy loss.
Universal hash functions
• Not a cryptographic hash
• Main purpose: uniformity
• Light-weight implementation in hardware and software.• Information-theoretic properties.
• Does not rely on unproven security assumptions
• Def: δ-almost universal hash functions Fr. For fixed x and x':
€
Prob[FR (x) = FR (x ')] ≤ 2−L (1+ δ)
Fr with random r
L bits
6
Fuzzy Extractor based on universal hash functions
secret key
redundancy forerror correction
MAC key
rp q
Key reconstruction procedure
• Measure x'. Read p', q', r', w', m'.
• Make list L of likely candidates. Must be manageable!
• Find x in L such that Ψp'(x)=w'.
Sort of Slepian-Wolf
• Compute v'=Γq'(x).
• Check if MAC(v'; p'q'r'w')=m'.
• If okay, reconstruct secret s=Φr'(x).
Publicly stored enrolment data: p,q,r,w, m:=MAC(v; pqrw)
attack
p', q', r', w', m'
7
Robustness: KMS-MAC
Theorem: If
then Δ(PQRWM S; PQRWM U) ≤ ε .
8
Robustness
•Ordinary MAC insufficient
•MAC with Key Manipulation Security? [Cramer et al, Eurocrypt 2008]
• Assumes strong attacker. Key Linearity: ΔK = known function of w and modified w'.
•We do not have the linearity property!(Also the case for other types of helper data.)Effect of modifying helper data unknown to attacker.
•KMS-MAC is overkill.
Part 2:
Simplification of Controlled PUF primitives
BŠ and Marc X. MakkesEindhoven University of Technology
9
Controlled PUFs (CPUFs)
•PUF shielded from the outside world by control layer
•control layer restricts PUF input & output
•more secure than "bare" PUF
Protocols exploiting large number of Challenge-Response Pairs
•Gassend et al 2002, 2007, 2008
•Each user has shared secret (CRP) with CPUF
•Symmetric crypto
•Certified Execution, Proof of Execution, key renewal, ...
•Presented as API code
• Self-referential 'hash blocks'
CPUF protocols
10
Simplification
• Avoid hashes of control layer code
• Flowchart notation
• Basically the same protocols; minor modifications
• Helper data explicitly visible
12
Some wise concluding remarks
Boris:
None of this is rocket science, and the results are far from spectacular ... so I will not complain if you don't put any of this in the schedule.
Ahmad:
(...) And we do not need rocket science. By the way, rocket science is very easy, this is a fairy-talethat rocket science is difficult. You buy some explosive powder and some metal container and you put them together.
13