Logic gates - Delaware Physicsmsafrono/311/Lecture15.pdf · 1 Quantum logic gates Logic gates...
Transcript of Logic gates - Delaware Physicsmsafrono/311/Lecture15.pdf · 1 Quantum logic gates Logic gates...
1
Quantum logic gates
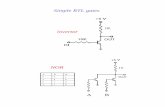
Logic gates
Classical NOT gateQuantum NOT gate
(X gate)
A N O T A
0 1
1 0
A NOT A
The only non-trivial
single bit gate
X10α β+ 01α β+
Matrix form representation
0 1
1 0X
=
Xβα
β α
=
2
More single qubit gates
Any unitary matrix U will produce a quantum gate!
Z0 1α β++++ 0 1α β−−−−1 0
0 1Z
= −
1 11
1 12
H
= −
H0 1α β+0 1 0 1
2 2α β
+ −+
Hadamard gate:
Single qubit gates,two-qubit gates,
three-qubit gates …
How many gates do we need to make?
Do we need three-qubit and four-qubit gates?
Where do we find such physical interactions?
Coming up with one suitable controlled interaction for
physical system is already a problem!
3
Universality:classical computation
Only one classical gate (NAND) is needed to
compute any function on bits!
A
BA AND B
A NOT A
A
BA NAND B
A B A AND B A NAND B
0 0 0 1
0 1 0 1
1 0 0 1
1 1 1 0
Universality:quantum computation
How many quantum gates do we need
to build any quantum gate?
Any n-qubit gate can be made from 2-qubit gates.
(Since any unitary n x n matrix can be decomposed to product
of two-level matrices.)
Only one two-qubit gate is needed!
Example: CNOT gate
4
Quantum Quantum Quantum Quantum CNOTCNOTCNOT
CNOT gategategategate
Quantum algorithms
Superposition: n qubits can represent 2n integers.
Problem: if we read the outcome we lose the superposition
and we can’t know with certainty which one of the values we
will obtain.
Entanglement: measurements of states of different
qubits may be highly correlated.
Unique features of quantum computation
5
Quantum algorithms
Strategy:
Use superposition to calculate 2n valuesof function simultaneously and
do not read out the result until a usefulresult is expected with reasonably high
probability.
Use entanglement
Quantum algorithms
Shor's quantum Fourier transform provides
exponential speedup over known classical algorithms.
Applications: solving discrete logarithm and factoring
problems which enables a quantum computer to break
public key cryptosystems such as RSA.
Quantum searching (Grover's algorithm) allows
quadratic speedup over classical computers.
Simulations of quantum systems.
6
Quantum cryptography
Classical cryptography
Scytale - the first known mechanical device to implement
permutation of characters for cryptographic purposes
7
Classical cryptography
Private key cryptography
How to securely transmit a private key?
Scientific American 314, 48-55 (2016)
8
Key distribution
A central problem in cryptography:
the key distribution problem.
1) Mathematics solution: public key cryptography.
2) Physics solution: quantum cryptography.
Public-key cryptography relies on the computational difficulty of certain hard mathematical problems
(computational security)
Quantum cryptography relies on the laws of quantum mechanics (information-theoretical security).
Basic idea of public key cryptosystems (much like a mailbox)
Alice sets a mailbox.Public key is available to the public
Public
Alice has secret key
Anyone can send mail
Only Alice can get the mail out of the mailbox
Result: anyone in the world can communicate with Alice privately.Note: there are two distinct keys; a public key and a private key (which only Alice has).
Private
Public key distribution
RSA cryptosystems
9
Suppose Bob wishes to send private message to Alice.
(1) Alice generates two keys, a public key (P) and a secret (private) key (S).
(2) Bob gets a copy of a public key (P).
(3) Bob encrypts the message using P. Encryption stage is very difficult to reverse!Like a trap door for the mail: if you put in your mail you can not get it out. Bob sends the encrypted message.
(4) Alice uses a secret key to decrypt the message.
Problem: There is no known scheme which is proven to be secure. It is just widely believed that it is!
How does it work?
Scientific American 314, 48-55 (2016)
10
Why public key encryption works?
Because some mathematical operations are easy
to do but very hard to undo:
The Mathematical Guts of RSA Encryption(http://fringe.davesource.com/Fringe/Crypt/RSA/Algorithm.html)
Multiply 18313 and 22307: 408 508 091 - Easy
Easy Easy
Easy
Now try to factor 408 508 091 back into these two numbers – Very hard
Very hardVery hard
Very hard
2014 factoring record: 1199
2014 factoring record: 11992014 factoring record: 1199
2014 factoring record: 1199-
--
-bit number (360 decimal digits)
bit number (360 decimal digits) bit number (360 decimal digits)
bit number (360 decimal digits)
7500 CPU-years on 2.2 GHz Opterons
For any positive integers
k is a non-negative integer and .
Modular arithmetic = ordinary arithmetic in which we pay attention to remaindersonly. Notation (mod n) is used to indicate that we are working in modular arithmetic.
Class exercise: Prove that 2=5=8=11 (mod 3)
How to factor numbers?
Modular arithmetic – working only with remainders
12
Classical factoring algorithm: How to factor 15?
(1) Pick a number less than 15 (for example 7).
(2) Calculate
How to factor numbers?
The point of calculating was to find period R. This is the step that is hard for classical computers for large n.
3) Calculate greatest common divisor
How to factor numbers?
13
Quantum factoring
Large-scale quantum computer will be able to break public-
key encryption.
Key distribution
A central problem in cryptography:
the key distribution problem.
1) Mathematics solution: public key cryptography.
2) Physics solution: quantum cryptography.
Public-key cryptography relies on the computational difficulty of certain hard mathematical problems
(computational security)
Quantum cryptography relies on the laws of quantum mechanics (information-theoretical security).